Increase Your Network Visibility for Detection and Response
Network-borne threats are difficult to detect, and legacy network protection tools and firewalls don’t always give you the full picture. Securonix NDR solves this by correlating security incidents across your entire IT environment with network activity and alerting your team to anomalies.

Read the Data Sheet
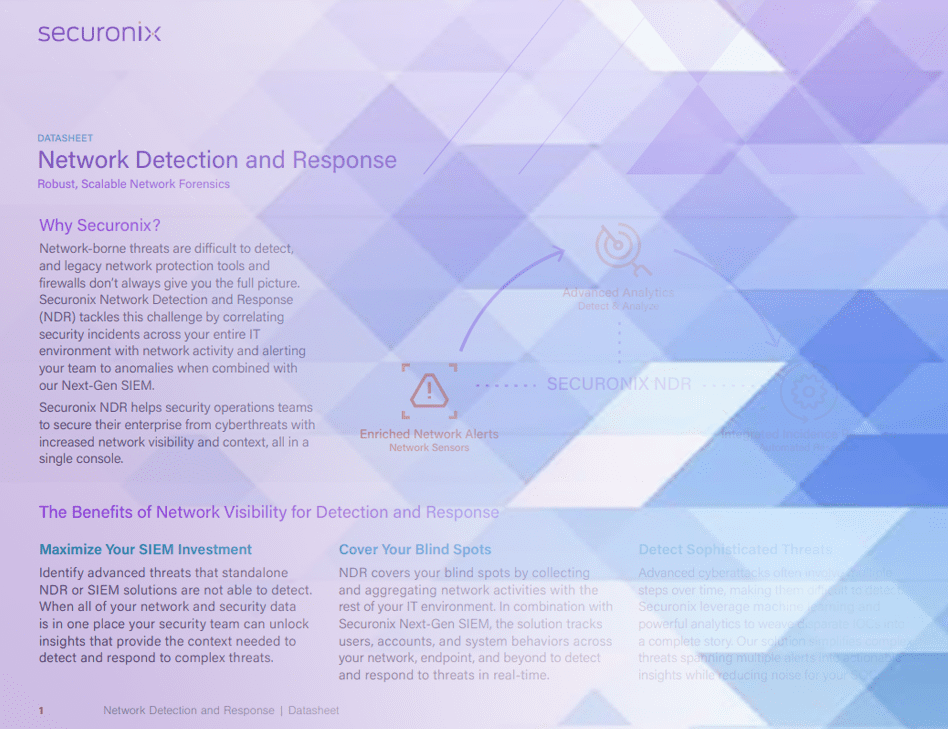
Network Detection and Response
Customers today struggle to detect the sophisticated slow and low attacks which require monitoring a blend of network traffic activity, user actions, and system behavior patterns. Stand-alone network traffic analysis tools can monitor traffic and detect network traffic anomalies, however, such anomalies without user and system context are less actionable and just add to the noise.Securonix provides you with a single platform that monitors and correlates network traffic events, security events, and user activities to detect the most advanced threats.
Download the datasheet to find out more.
Why Securonix for Network and Response?
Network

Cover Your Blind Spots
Endpoint and log data alone doesn’t give you the full picture of risk in your organization. NDR covers these blind spots by collecting and aggregating network activities with the rest of your IT environment.
Network Sensors: Combine data from third-party network sensors (including Corelight, Verizon, and Gigamon) with other security data to enrich your SIEM with an extra layer of insight.
Threat Hunting: Empower threat hunters to connect the dots faster with 360-degree visibility of log, endpoint, and network data.
Detect
Detect Sophisticated Threats
Threat Chains: Leverage identity context to help you trace low and slow threats that span across your network and security events.
Advanced Analytics: Understand when network behaviors are deviating from established baselines with minimal noise.

Visibility

Gain Complete Visibility Into Your Network Data
Single Platform: Reduce operational complexity with a single, fully integrated backend architecture and zero infrastructure to manage. Robust Reporting: Leverage reports on network traffic and built-in, shareable dashboards to make data-informed decisions.
Read The Whitepaper
NDR Belongs in Your Security Operations Center
NDR solutions reduce mean time to detect (MTTD) and mean time to respond (MTTR) by providing network and contextual data to aid in investigations.
If you would like more information on Securonix, contact us today!